In today’s rapidly evolving digital landscape, businesses face increasing threats from cybercriminals. From data breaches to ransomware attacks, the risks are growing in both frequency and sophistication. This is where cybersecurity asset management play a vital role. These specialized firms help organizations protect sensitive data, maintain compliance, and ensure business continuity.
This article explores the importance of IT security companies, their services, benefits, and how to choose the right partner for your organization.
What Are IT Security Companies?
IT security companies are organizations that specialize in protecting digital infrastructure, networks, systems, and data from cyber threats. They provide a wide range of cybersecurity services designed to detect, prevent, and respond to potential attacks.
These companies serve businesses of all sizes, from startups to large enterprises, across various industries such as healthcare, finance, retail, and manufacturing.
Why Businesses Need IT Security Companies
Cybersecurity is no longer optional. With the rise of remote work, cloud computing, and digital transformation, businesses are more vulnerable than ever.
Here are key reasons why companies rely on IT security providers:
1. Increasing Cyber Threats
Cyberattacks such as phishing, malware, and ransomware are becoming more advanced. IT security companies help identify vulnerabilities before attackers exploit them.
2. Data Protection
Sensitive information, including customer data and financial records, must be protected. Security companies ensure data encryption, secure storage, and safe transmission.
3. Regulatory Compliance
Many industries require strict compliance with regulations like GDPR, HIPAA, and ISO standards. IT security firms help organizations meet these requirements.
4. Business Continuity
Cyber incidents can disrupt operations. Security companies implement disaster recovery and incident response strategies to minimize downtime.
Core Services Offered by IT Security Companies
IT security companies offer a wide range of services tailored to different business needs.
1. Network Security
They protect internal and external networks from unauthorized access using firewalls, intrusion detection systems, and monitoring tools.
2. Endpoint Protection
This involves securing devices such as laptops, desktops, and mobile phones against malware and unauthorized access.
3. Cloud Security
As businesses move to cloud platforms, IT security companies ensure data stored in the cloud remains secure and compliant.
4. Threat Detection and Response
Advanced tools and AI-driven systems detect unusual activity in real time and respond quickly to mitigate risks.
5. Vulnerability Assessment and Penetration Testing
Security experts identify weaknesses in systems and simulate cyberattacks to test defenses.
6. Security Awareness Training
Employees are often the weakest link in cybersecurity. Training programs educate staff on recognizing and avoiding threats.
Benefits of Hiring IT Security Companies
Partnering with a reliable IT security company offers several advantages:
1. Expertise and Experience
These companies have skilled professionals who stay updated with the latest threats and technologies.
2. Cost Efficiency
Hiring an in-house security team can be expensive. Outsourcing to IT security companies reduces operational costs.
3. 24/7 Monitoring
Continuous monitoring ensures that threats are detected and addressed immediately.
4. Advanced Technology
IT security firms use cutting-edge tools and technologies that may not be affordable for individual businesses.
5. Peace of Mind
Knowing your systems are protected allows you to focus on core business activities.
How to Choose the Right IT Security Company
Selecting the right partner is crucial for effective cybersecurity. Consider the following factors:
1. Industry Experience
Choose a company with experience in your specific industry.
2. Range of Services
Ensure the company offers comprehensive services that match your needs.
3. Certifications and Compliance
Look for certifications such as ISO 27001, CISSP, or CEH, which indicate expertise and reliability.
4. Customization
A good IT security company provides tailored solutions rather than a one-size-fits-all approach.
5. Reputation and Reviews
Check client testimonials and case studies to evaluate performance.
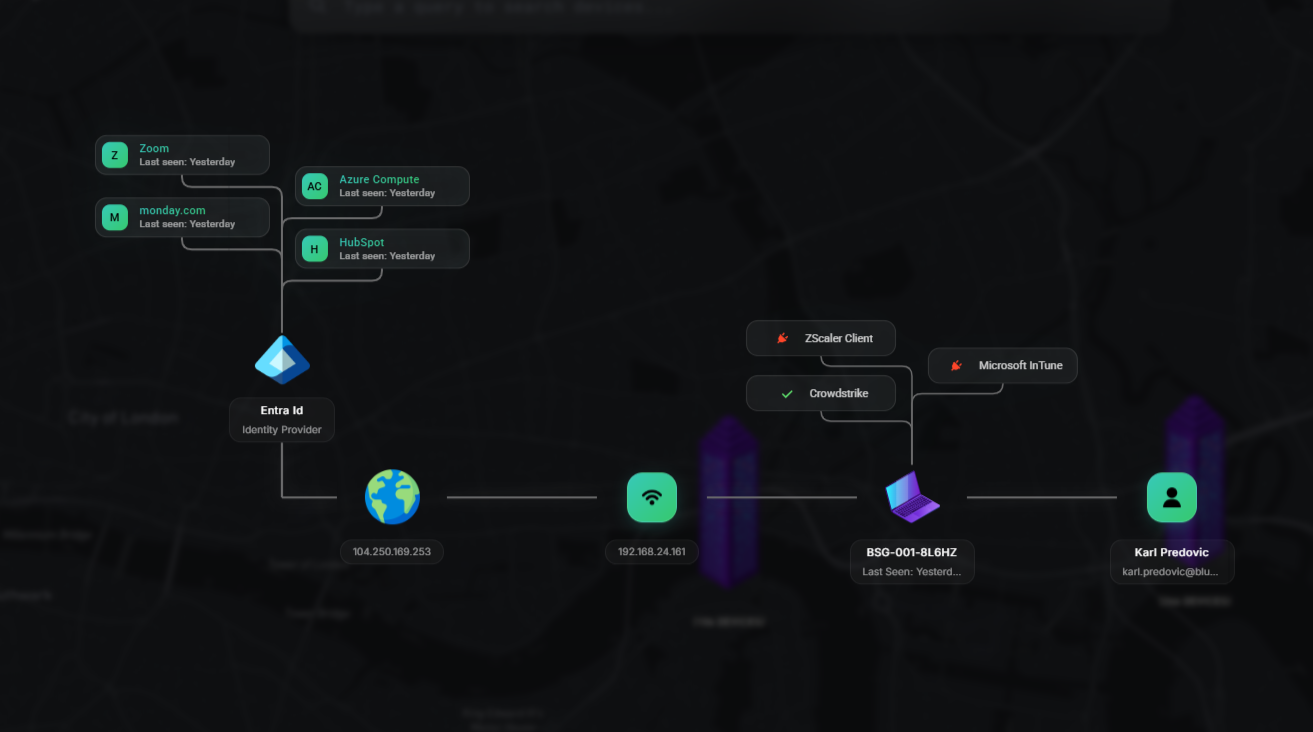
The Role of Centralized Cybersecurity Platforms
Modern IT security companies often use centralized platforms to manage and protect IT assets efficiently. These platforms provide a unified view of an organization’s security posture.
For example, solutions like ThreatAware’s centralized cybersecurity platform allow businesses to:
Monitor all IT assets from a single dashboard
Detect vulnerabilities in real time
Automate security processes
Improve compliance management
By using such platforms, companies can streamline their cybersecurity operations and respond faster to threats.
Trends Shaping IT Security Companies
The cybersecurity landscape is constantly evolving. Here are some key trends:
1. Artificial Intelligence and Machine Learning
AI-powered tools help detect anomalies and predict potential threats more accurately.
2. Zero Trust Security Model
This approach assumes no user or system is trusted by default, enhancing security.
3. Cloud-First Security
As more businesses adopt cloud solutions, security strategies are shifting accordingly.
4. Managed Security Services (MSS)
Many companies prefer outsourcing security operations to managed service providers for better efficiency.
Common Challenges in Cybersecurity
Despite advancements, businesses still face several challenges:
Lack of skilled cybersecurity professionals
Increasing complexity of IT environments
Budget constraints
Evolving cyber threats
IT security companies help overcome these challenges by providing expertise, tools, and strategic guidance.
Conclusion
IT security companies are essential partners in today’s digital world. They help businesses protect their assets, maintain compliance, and stay ahead of cyber threats. By offering advanced tools, expert knowledge, and continuous monitoring, these companies ensure a strong defense against potential attacks.











Write a comment ...